Penetration testing follows a structured methodology designed to simulate real cyberattacks and measure how well systems withstand them. A VAPT (Vulnerability Assessment and Penetration Testing) engagement moves through defined phases that identify vulnerabilities, validate exploitability, and analyze potential business impact. Security teams examine applications, networks, APIs, and cloud environments to uncover weaknesses that attackers could use to gain unauthorized access.
The process combines automated vulnerability discovery with manual attack simulation. Tools such as Nmap, Burp Suite, and Metasploit help map the attack surface and test defenses. Each phase builds on the previous one, turning raw findings into verified security risks and clear remediation guidance for improving overall security posture.
What the VAPT Methodology Is Designed to Achieve?
The objective of VAPT methodology is to reveal how exposed an organization is to real cyber threats. Many organizations rely on professional VAPT services to simulate realistic attack scenarios and identify weaknesses across networks, applications, APIs, and cloud infrastructure. Structured testing shows how threat actor behavior interacts with existing security controls and where defenses may fail.
As cyber threats continue to rise, organizations face unprecedented risk. Global cybercrime damages are expected to reach $10.5 trillion annually by 2025, while the average data breach now costs businesses over $4.4 million, making proactive security validation essential.
A well executed penetration testing process goes beyond simple vulnerability discovery. It validates exploitability, measures risk exposure, and evaluates whether an attacker could move from an initial weakness to a larger breach.
For example, a misconfigured access control rule might appear minor during scanning, yet controlled exploit validation could expose sensitive data. Such testing provides a realistic security posture assessment and clear insight into potential breach simulation paths.
The Two Execution Mindsets Inside VAPT
Two complementary approaches drive the VAPT process. Vulnerability assessment focuses on detection. Security teams use vulnerability scanners to identify potential issues such as outdated software, weak authentication, or configuration flaws. Automated discovery often produces false positives, so findings require careful review.
Penetration testing focuses on exploitation. Testers manually validate vulnerabilities to determine whether they can be used in an attack chain. Proof of concept exploitation may demonstrate privilege escalation, credential compromise, or remote code execution.
The difference between scanning and penetration testing lies in that validation. Detection reveals possible weaknesses, while exploitation confirms whether they pose real security risk.
The Complete VAPT Methodology Lifecycle (Step-by-Step Execution Flow)
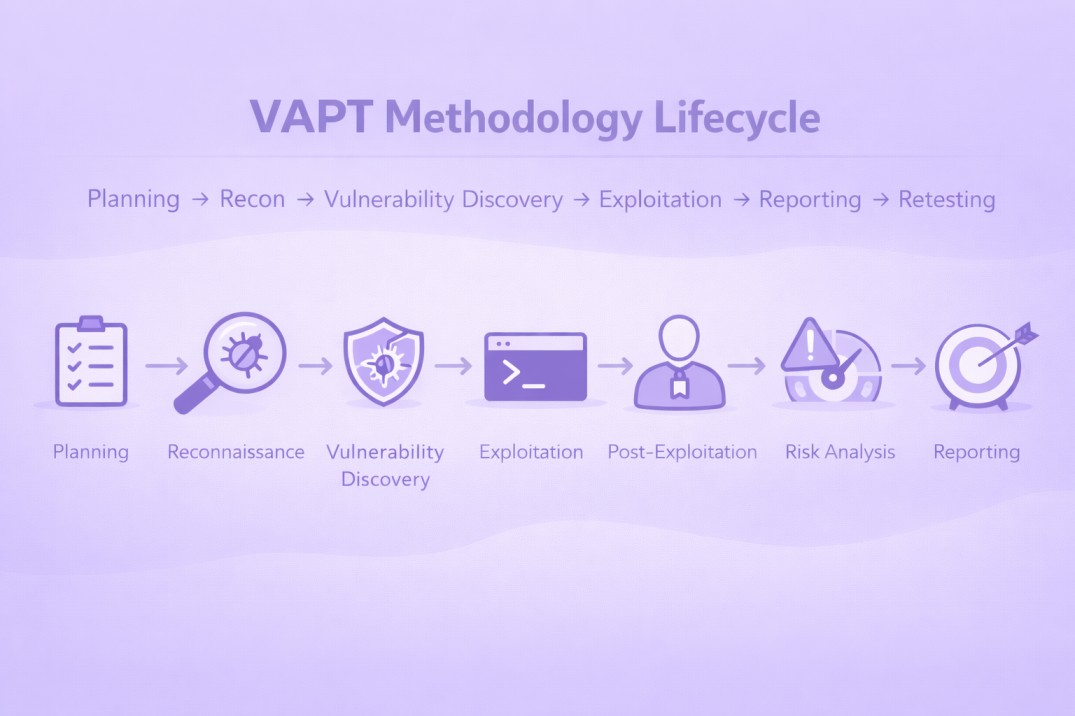
The VAPT methodology lifecycle explains how a professional penetration testing engagement unfolds from preparation to remediation. Each phase builds on the previous one, allowing security teams to move from attack surface discovery to verified risk exposure and finally to actionable remediation.
The need for structured testing continues to grow. In 2025, studies show that over 67% of enterprises experienced a cyber breach within the last two years, highlighting the importance of continuous vulnerability validation and penetration testing.
A structured penetration testing lifecycle process usually includes planning, reconnaissance, vulnerability assessment, controlled exploitation, impact analysis, risk scoring, reporting, and retesting.
Following a defined VAPT process flow helps testers simulate realistic attack scenarios while keeping testing controlled and authorized. The result is a clear understanding of how an attacker could move through the environment and which vulnerabilities require immediate attention.
Phase 1 (Pre-Engagement Planning and Scope Definition)
The pre engagement phase in penetration testing establishes the rules and boundaries of the assessment. Security teams and the organization agree on the penetration testing scope, define systems to be tested, and document legal authorization for the engagement.
Key elements include creating a scope document, signing an NDA, and establishing rules of engagement. These steps prevent accidental disruption and ensure testing remains compliant with internal policies and regulatory requirements.
A clear engagement charter also defines testing timelines, communication channels, and escalation procedures if critical vulnerabilities are discovered.
Defining the Attack Surface
The first task involves identifying the attack surface. Security teams map all assets that may be exposed to attackers, including subdomains, IP ranges, APIs, cloud instances, and externally exposed services.
For example, an organization might intend to test only a web application, yet reconnaissance may reveal forgotten subdomains or open API endpoints. Mapping the full attack surface ensures penetration testers evaluate the same entry points a real attacker would discover.
Black Box vs White Box vs Grey Box Approach
Penetration testing methodology also depends on the level of knowledge provided to testers.
Black box testing simulates an external attacker with zero prior knowledge. Testers begin with only public information and attempt to discover vulnerabilities from the outside.
White box testing provides full insider knowledge, including architecture details, source code, and credentials. Security teams analyze the environment deeply and identify hidden weaknesses.
Grey box testing sits between the two approaches. Limited credentials or partial documentation help testers simulate a realistic attacker who has already gained some level of access.
Phase 2 (Reconnaissance and Attack Surface Mapping)
The reconnaissance phase in penetration testing focuses on collecting intelligence about the target environment. Security teams perform information gathering to understand how systems are exposed, which technologies are running, and where potential entry points exist.
Reconnaissance often begins with OSINT (Open Source Intelligence). Public data such as DNS records, WHOIS information, employee details, and technology fingerprints reveal valuable insights about infrastructure.
Tools like Shodan help identify exposed services, while scanners such as Nmap assist with service discovery and port enumeration.
The goal is accurate attack surface mapping. Testers identify reachable servers, APIs, subdomains, and network services that could become attack vectors.
For example, a forgotten development subdomain might expose outdated software or weak authentication controls.
Effective reconnaissance reduces guesswork. It allows penetration testers to build a realistic attack chain, guiding later phases such as vulnerability discovery and controlled exploitation.
Phase 3 (Vulnerability Assessment and Validation)
The vulnerability assessment phase identifies weaknesses that attackers could exploit. Security teams analyze systems for software vulnerabilities, misconfigurations, authentication flaws, injection risks, and outdated components. Automated tools assist discovery, while manual analysis verifies accuracy.
Common techniques include vulnerability scanners, configuration reviews, and dependency analysis. Testers often reference databases such as CVE (Common Vulnerabilities and Exposures) to match discovered issues with known security flaws. Security frameworks from OWASP and NIST guide testing priorities and risk evaluation.
Validation is critical. Automated scanners may flag issues that are not exploitable in practice. Security professionals manually confirm findings to eliminate false positives and identify access control weaknesses or insecure patch management practices.
The result is a verified list of vulnerabilities that may expose systems to real attacks. Each confirmed weakness becomes a candidate for the next stage, where penetration testers attempt controlled exploitation to demonstrate actual security impact.
Phase 4 (Exploitation and Controlled Attack Simulation)
The exploitation phase in penetration testing demonstrates whether identified vulnerabilities can be used in a real attack. Security testers move beyond detection and perform controlled attack simulation to validate exploitability without harming production systems.
Testers craft payloads and attempt techniques such as remote code execution, session hijacking, credential reuse, or privilege escalation. Tools like Metasploit help automate exploit delivery, while manual techniques allow testers to combine weaknesses into an attack vector or vulnerability chain.
For example, an injection vulnerability in a web application might first expose user credentials. Those credentials could then allow lateral movement into internal systems. Such chained exploitation reveals how attackers escalate access.
Each successful attempt is documented as a proof of concept, showing how a vulnerability can lead to real compromise and measurable security risk.
Phase 5 (Post Exploitation and Impact Analysis)
After successful exploitation, testers evaluate what an attacker could achieve with the obtained access. The post exploitation phase in VAPT focuses on understanding business impact, not just technical compromise.
Security teams analyze whether the attacker can reach sensitive data, maintain persistence, or expand access across systems. Activities may include checking for privilege abuse, accessing confidential databases, or testing whether compromised credentials allow deeper access expansion within the environment.
The objective is realistic breach simulation. For example, gaining low-level access to a server may appear limited, yet poor privilege separation could allow escalation to administrator control and exposure of critical data.
Such analysis helps organizations see how a single vulnerability can lead to data exposure, compliance risk, or full system compromise, enabling clearer remediation priorities.
Phase 6 (Risk Scoring and Severity Classification)
Once vulnerabilities are confirmed, security teams determine how dangerous each issue actually is. The vulnerability severity classification process prioritizes findings based on real risk and remediation urgency.
Most penetration testing reports rely on the CVSS (Common Vulnerability Scoring System) developed by FIRST. CVSS evaluates several factors including exploitability metrics, impact metrics, and the base score of the vulnerability. Environmental factors may also adjust the environmental score to reflect business context.
For example, a vulnerability allowing remote code execution on a public server may receive critical severity, while the same issue on an isolated internal system could receive a lower score.
Accurate risk prioritization helps organizations focus on vulnerabilities that expose the greatest security risk, ensuring remediation efforts address the most dangerous weaknesses first.
Phase 7 (Reporting and Documentation)
The VAPT report turns technical findings into clear security intelligence for both engineers and leadership. A well structured penetration testing report format explains what was discovered, how vulnerabilities were exploited, and why they matter to the business.
Reports usually begin with an executive summary that outlines overall security posture and major risks. The technical section then details each finding with evidence documentation, reproduction steps, and a clear impact statement. Screenshots, logs, and proof-of-concept data support every verified vulnerability.
Each issue receives a risk rating based on severity and exploitability. Practical remediation guidance follows, helping security teams patch vulnerabilities, strengthen access controls, or improve system configuration.
Clear documentation ensures stakeholders understand the risk and can prioritize fixes without ambiguity.
Phase 8 (Remediation Validation and Retesting)
Security improvements are not complete until fixes are verified. The final step in the VAPT process involves remediation validation and retesting to confirm that vulnerabilities have been properly resolved.
Security teams perform validation testing after patches or configuration changes are applied. Testers repeat the original attack steps to confirm that the weakness no longer exists. In many cases, regression testing is also performed to ensure that new changes did not introduce additional vulnerabilities.
For example, if a SQL injection vulnerability was fixed through input validation and patch updates, testers attempt the same exploit again to verify the fix. Successful remediation results in patch verification and remediation confirmation.
Retesting provides measurable proof of security improvement and ensures the organization’s defenses have genuinely strengthened after the VAPT engagement.
How VAPT Methodology Adapts Across Different Environments?
The VAPT methodology adapts based on the environment being tested. Attack surfaces vary across web applications, APIs, cloud infrastructure, and internal networks, so penetration testers adjust their techniques to match the architecture and threat model.
Web Application Penetration Testing
Web applications often expose the largest public attack surface. Testers focus on vulnerabilities listed in the OWASP Top 10, especially issues related to authentication, session management, and user input handling.
Primary testing focus:
Input validation and injection vulnerabilities
Authentication and session management flaws
Broken access control
Cross-site scripting and data exposure
Typical testing tools:
Burp Suite
OWASP ZAP
Custom payload testing
API Security Testing
Modern applications rely heavily on REST APIs and microservices, which introduce different security risks. APIs often expose backend logic directly, making authorization flaws easier to exploit.
Primary testing focus
Broken authentication
Broken object level authorization
Excessive data exposure
Weak API rate limiting
Cloud Penetration Testing
Cloud environments introduce unique attack surfaces across identity systems, storage services, containers, and virtual machines. Misconfigurations are one of the most common causes of cloud breaches.
The demand for cloud security testing continues to grow rapidly as organizations migrate infrastructure online. The global penetration testing market reached approximately $2.7 billion in 2025, reflecting increased investment in proactive security validation.
Primary testing focus:
Misconfigured cloud storage buckets
Weak identity and access management (IAM)
Exposed management ports
Container and orchestration security
Internal Network Penetration Testing
Internal testing evaluates how far an attacker could move after gaining initial access to a corporate network. The goal is to simulate lateral movement and privilege escalation inside the environment.
Primary testing focus:
Weak Active Directory permissions
Credential reuse
Insecure file shares
Privilege escalation paths
DevSecOps and Continuous Security Testing
Modern organizations integrate security testing into CI/CD pipelines through DevSecOps practices. Automated checks run during development to detect vulnerabilities before deployment.
Continuous validation supports zero trust architecture, allowing security teams to identify weaknesses early and maintain a strong security posture as systems evolve.
Operational Realities During a VAPT Engagement
A VAPT engagement rarely follows a perfectly smooth path. Real environments introduce constraints that influence how penetration testing is performed. Understanding these operational realities helps organizations set realistic expectations for results.
One common challenge involves scope restrictions. Security teams can test only the assets listed in the scope document, even if reconnaissance reveals additional systems. Expanding scope requires formal approval to avoid legal or operational risks.
Another factor is defensive technology. Tools such as Web Application Firewalls (WAFs), intrusion detection systems, and rate limiting controls may block testing activity. Testers often adjust techniques to safely simulate attacks without disrupting production services.
Testing also occurs under time constraints. Many engagements last only a few days or weeks, which means the assessment represents a focused evaluation rather than an exhaustive security review. Careful planning ensures the most critical attack paths receive attention while maintaining system stability.
Common Limitations of VAPT Methodology
Even a well planned VAPT methodology has practical limits. Penetration testing reveals real vulnerabilities and validates exploitability, yet it cannot guarantee complete protection. Security environments evolve continuously, while VAPT evaluates systems within defined boundaries and timeframes.
Snapshot Nature of Security Testing
A VAPT engagement provides a point in time security assessment. Systems, applications, and infrastructure change as updates, new APIs, and configuration adjustments appear. A system considered secure during testing may expose new weaknesses later. Regular security validation helps maintain an accurate security posture assessment.
Zero Day and Unknown Vulnerabilities
Penetration testers rely on known attack techniques, public vulnerability databases, and realistic exploit patterns. Completely unknown flaws, known as zero-day vulnerabilities, may remain undiscovered during testing. Attackers sometimes identify these weaknesses first, which is why organizations combine VAPT with threat intelligence and continuous monitoring.
Scope and Time Constraints
Every engagement follows a defined scope document and testing schedule. Only the approved assets, such as specific applications, IP ranges, or APIs, can be evaluated. Limited testing windows also restrict how deeply testers explore complex attack paths. VAPT therefore focuses on the most critical attack surface exposure rather than every possible system.
VAPT Is Not Continuous Security
VAPT strengthens defenses, yet it does not replace ongoing protection. New vulnerabilities appear as technologies evolve and systems grow. Effective organizations combine VAPT with continuous security testing, vulnerability scanning, and proactive defense improvement to maintain long term resilience against modern threats.
What Makes a VAPT Methodology Truly Effective?
An effective VAPT methodology does more than identify vulnerabilities. The real value comes from how accurately the test reflects real attack behavior and how clearly the results guide security improvements. Strong engagements combine structured methodology, skilled manual analysis, and realistic attack simulation to reveal exploitable weaknesses.
Realistic Attack Simulation
Effective penetration testing mirrors how threat actors operate. Testers simulate real attack paths, combining multiple weaknesses to expose attack chains that automated scans often miss. For example, a small authentication flaw may lead to privilege escalation when combined with weak access control.
Depth of Manual Testing
Automated scanners detect many vulnerabilities, yet they cannot fully evaluate business logic flaws or complex security misconfigurations. Skilled testers perform manual validation and exploit development to confirm whether a vulnerability truly exposes risk.
Continuous Security Validation
Security testing becomes far more effective when performed regularly rather than as a one-time activity. Organizations that integrate testing into DevSecOps workflows, vulnerability management, and periodic VAPT engagements maintain stronger security maturity and reduce long term breach risk.
Frequently Asked Questions
What is VAPT in cybersecurity?
VAPT stands for Vulnerability Assessment and Penetration Testing. It is a security testing approach used to identify vulnerabilities and simulate cyberattacks to evaluate how well systems can resist real world threats.
What are the main phases of the VAPT methodology?
The VAPT methodology typically includes planning, reconnaissance, vulnerability assessment, exploitation, post exploitation analysis, risk scoring, reporting, and remediation validation.
What is the difference between vulnerability assessment and penetration testing?
Vulnerability assessment identifies potential security weaknesses through scanning and analysis. Penetration testing validates those weaknesses by attempting controlled exploitation to determine real security impact.
What tools are commonly used during penetration testing?
Security teams often use tools such as Nmap for network discovery, Burp Suite for web application testing, Metasploit for exploitation, and OWASP ZAP for vulnerability analysis.
What environments can be tested using VAPT methodology?
VAPT methodology can be applied to web applications, APIs, cloud infrastructure, internal networks, mobile applications, and enterprise systems to identify potential security risks.
Why is VAPT important for cybersecurity?
VAPT helps organizations detect vulnerabilities before attackers exploit them. By simulating real attack scenarios, it provides clear insights into security weaknesses and supports effective remediation.


