API security testing is the process of evaluating whether an Application Programming Interface can be accessed, manipulated, or abused beyond its intended design. It verifies that authentication, authorization, input validation, and data exposure controls work correctly at the endpoint level.
In practice, many organizations complement internal testing efforts with API Security Scan Services to gain independent validation of these controls.
Since APIs directly expose application logic and data over HTTP, even small flaws can allow unauthorized access, privilege escalation, or large-scale data extraction. API security testing identifies those weaknesses before attackers exploit them.
Why API Security Testing Matters in Modern Architecture?
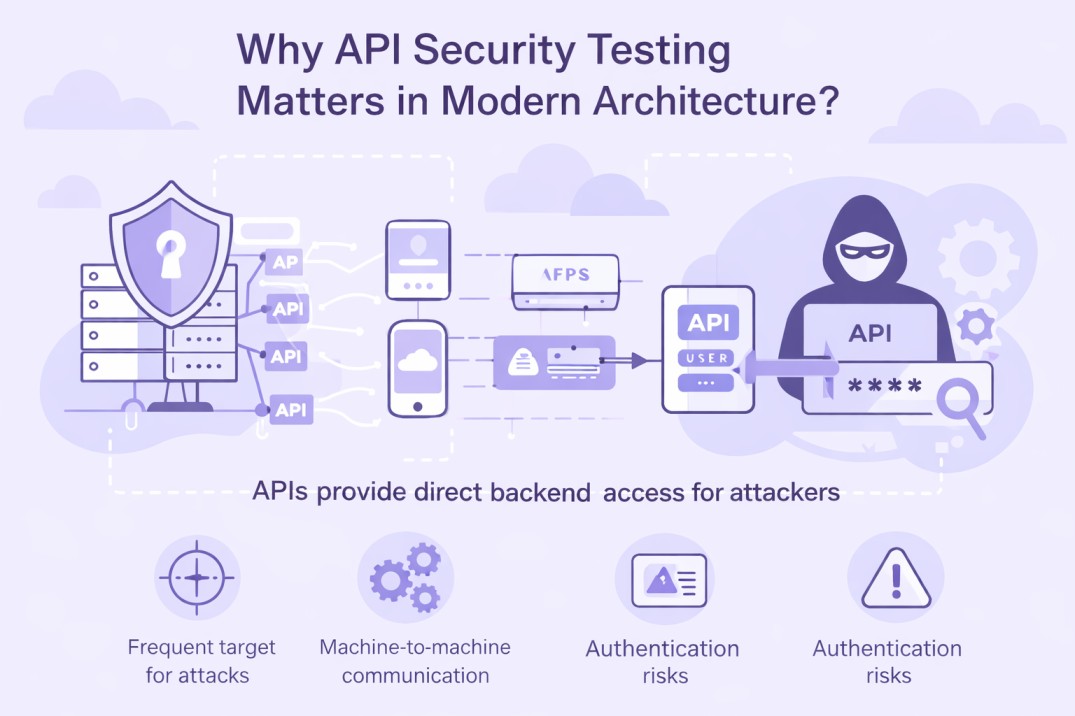
Modern applications run on APIs. Web apps, mobile apps, SaaS platforms, and partner integrations communicate through API endpoints. In API first and microservices environments, backend systems are exposed through multiple programmatic interfaces rather than a single web layer. Each exposed endpoint increases the attack surface.
According to the 2025 State of API Security Report, 99% of organizations reported experiencing API security problems in the past year, highlighting how widespread API exposure has become.
APIs Provide Direct Backend Access
APIs are designed for machine to machine communication. Attackers can send crafted HTTP (Hypertext Transfer Protocol) requests directly to endpoints without using a browser interface. In 2025, APIs received 43% more attacks than traditional web applications, reinforcing that attackers increasingly target backend interfaces rather than user-facing pages.
If authentication or authorization checks are incomplete, modifying request parameters may expose restricted data or trigger unauthorized actions. Frontend controls do not protect server-side weaknesses.
Microservices and Cloud Architectures Expand Exposure
Modern environments rely on:
Public APIs for customer applications
Internal APIs between services
Partner APIs for external integrations
Mobile applications using persistent access tokens
APIs Control High Value Business Operations
Critical functions often operate at the API layer:
Login and session validation
Payment processing
Account management
Data retrieval and modification
Administrative actions
For example, if an API endpoint returns user data based solely on an ID parameter without verifying ownership, changing the identifier may expose another user’s records. Such issues occur at the authorization layer, not the user interface.
API Specific Risks Are Widely Recognized
In 2025, 84% of security professionals reported at least one API security incident in the previous 12 months, with broken authorization and authentication flaws among the leading causes. Security research and frameworks such as the OWASP (Open Worldwide Application Security Project) API Top 10 identify recurring API weaknesses, including:
Broken Object Level Authorization
Broken Authentication
Excessive Data Exposure
Lack of Rate Limiting
Security Misconfiguration
API Security Testing vs Other Security Practices

The term “API security testing” is often used loosely. It overlaps with API testing, vulnerability scanning, and penetration testing. Clear boundaries help teams choose the right approach and avoid gaps in coverage.
API Security Testing vs Functional API Testing
Functional API testing verifies that endpoints work as intended. It checks whether the API returns the correct response, handles expected inputs, and meets performance requirements.
API security testing asks a different question:
“Can the endpoint be abused?”
Functional testing confirms that a login endpoint authenticates valid users. Security testing verifies that invalid tokens are rejected, expired JWTs cannot be reused, and users cannot access another account by modifying an identifier.
One focuses on correctness. The other focuses on resilience under malicious conditions.
API Security Testing vs Vulnerability Scanning
API vulnerability scanning uses automated tools to detect known weaknesses such as SQL (Structured Query Language) injection patterns, missing security headers, or exposed debug endpoints.
Automated scanning provides breadth. It identifies common issues quickly across many endpoints.
API security testing goes deeper. It evaluates context-specific risks such as:
Broken Object Level Authorization
Role escalation across tenants
Workflow manipulation
Insecure token handling
API Security Testing vs API Penetration Testing
API penetration testing attempts to exploit vulnerabilities to demonstrate real impact. It often involves chaining weaknesses together to simulate attacker behavior.
API security testing is broader and more structured. It systematically validates authentication, authorization, input controls, rate limiting, and data exposure across the API surface.
Penetration testing proves exploitation. Security testing ensures controls are correctly implemented before exploitation occurs.
API Security Testing vs Runtime API Protection
Runtime API protection tools monitor live traffic. They detect anomalies, bot activity, and abuse patterns in production environments.
API security testing occurs before or alongside deployment. It identifies misconfigurations and design flaws during development or staging.
Testing prevents vulnerabilities from reaching production. Runtime protection responds when abuse occurs.
Despite rising threats, only 21% of organizations report having strong detection capabilities at the API layer, and just 13% believe they can prevent the majority of API attacks.
Understanding the API Attack Surface

More than 40,000 API security incidents were recorded globally in the first half of 2025 alone, reflecting a sharp rise in targeted API abuse. Effective API security testing begins with visibility. Security teams cannot protect endpoints that are undocumented, deprecated, or unintentionally exposed. Many API breaches occur because organizations lack a complete inventory of accessible endpoints.
An API attack surface includes every endpoint, version, authentication flow, and integration point that can be reached directly or indirectly.
API Inventory and Discovery
Security testing starts with identifying all active APIs, including:
Public APIs exposed to customers
Internal APIs used between microservices
Partner or third party integration APIs
Deprecated or legacy versions that remain accessible
Development or staging endpoints exposed unintentionally
API discovery often involves reviewing OpenAPI or Swagger specifications, analyzing API gateway logs, and performing controlled endpoint enumeration. Documentation alone is rarely complete.
Undocumented endpoints are commonly referred to as shadow APIs. They expand the attack surface without monitoring or formal access control review.
Versioning and Endpoint Sprawl
Organizations frequently maintain multiple API versions. Older versions may lack updated validation logic, stronger authentication controls, or recent security fixes.
Security testing should evaluate:
Versioned routes such as /v1/, /v2/, or /beta/
Deprecated endpoints that still respond to requests
Inconsistent authorization rules across versions
Trust Boundaries and Integration Points
APIs operate across different trust zones:
Client to server communication
Service to service communication
External partner integrations
Each boundary introduces assumptions about identity and authorization. API security testing validates that these assumptions are enforced server-side.
For example, an internal API may rely on network level trust rather than token validation. If exposed externally through misconfiguration, it may lack proper authentication checks.
Core Pillars of API Security Testing
API security testing is not a single activity. It evaluates multiple control layers that protect data and business logic. Each layer represents a boundary attackers attempt to bypass.
A structured approach examines identity, access control, input handling, output exposure, abuse resistance, and workflow integrity.
Authentication Testing (Verifying Identity)
Authentication confirms who is making a request. If identity verification fails, all other controls lose meaning.
Security testing evaluates:
JWT signature validation
Token expiration and renewal logic
OAuth 2.0 authorization flows
API key handling
Replay attack resistance
Weak or hardcoded secrets
For example, if an API accepts expired tokens or fails to validate a JWT signature, an attacker may forge credentials and gain unauthorized access.
Authentication testing ensures tokens, sessions, and credentials are validated strictly at the server level.
Authorization Testing (Enforcing Access Boundaries)
Authorization determines what an authenticated user is allowed to access.
Common failures include:
Broken Object Level Authorization (BOLA)
Broken Function Level Authorization (BFLA)
Insecure Direct Object References (IDOR)
Privilege escalation
Weak role enforcement
Testing involves modifying object identifiers, roles, or request parameters to verify ownership validation and multi tenant isolation.
For example, changing a user ID in a request should not return another user’s data. Proper authorization enforcement validates object ownership before returning results.
Input Validation and Injection Resistance
APIs process structured input such as JSON or XML (Extensible Markup Language) payloads. Weak validation allows malicious data to alter backend behavior.
Testing covers:
SQL injection
NoSQL injection
Command injection
XML External Entity (XXE)
Server Side Request Forgery (SSRF)
Mass assignment vulnerabilities
For instance, if an API automatically maps JSON fields to database models, adding an unexpected field such as "role": "admin" may elevate privileges.
Strong schema validation and strict input controls reduce injection and manipulation risks.
Excessive Data Exposure and Response Security
APIs often return more data than necessary. Sensitive fields may be included unintentionally.
Security testing verifies:
Field level authorization
Removal of internal identifiers
Filtering of sensitive attributes
Avoidance of debug information in production responses
For example, returning password hashes, internal IDs, or hidden metadata creates unnecessary exposure even if authentication is correct. Data minimization and response filtering are essential API security controls.
Rate Limiting and Abuse Resistance
APIs are designed for automation. Without request controls, attackers can exploit endpoints at scale.
Testing evaluates:
Rate limiting thresholds
Brute force protection
Enumeration resistance
Resource exhaustion controls
Distributed request handling
If login endpoints lack throttling, automated credential stuffing attacks become feasible. Rate limiting ensures APIs remain resilient under abnormal request patterns. As AI-driven automation expands, 51% of developers now express concern about unauthorized or excessive API calls generated by AI agents, introducing a new class of abuse risk.
Business Logic and Workflow Integrity Testing
Business logic vulnerabilities are application-specific and often missed by automated tools.
Testing focuses on:
Multi step workflow bypass
Payment manipulation
Discount or coupon abuse
State transition flaws
Skipping mandatory verification steps
For example, if a checkout API calculates price based on a client supplied parameter rather than server side validation, modifying the value may reduce payment amounts.
Business logic testing validates that the API enforces intended rules under unexpected request sequences.
REST vs GraphQL vs SOAP (How Testing Approaches Differ)
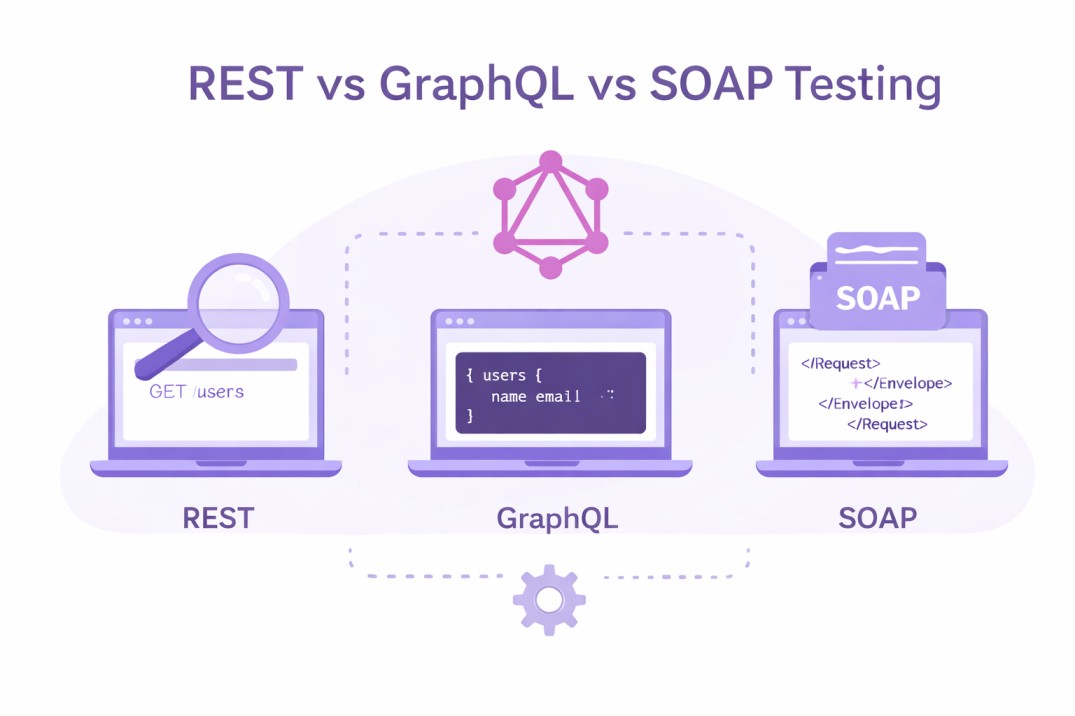
Not all APIs behave the same way. The protocol and design model directly influence how security weaknesses appear. Testing strategies must adapt to those differences.
An endpoint-based REST API presents risks differently than a query-driven GraphQL API. SOAP(Simple Object Access Protocol) introduces its own XML related concerns. Treating them identically leads to blind spots.
REST APIs (Endpoint Centric Risk)
REST APIs expose multiple URLs, each tied to a resource. The attack surface is distributed across endpoints such as:
/api/users
/api/orders
/api/admin/reports
Risk often hides in predictable patterns. Common REST specific testing angles include:
Manipulating object identifiers in URLs
Changing HTTP methods such as switching GET to PUT
Injecting unexpected JSON fields
Testing inconsistent access controls across versions
A common failure scenario involves object ownership. If /api/users/1050 returns user data without verifying the requesting user's identity, altering the ID becomes an easy data extraction method.
REST testing requires endpoint-by-endpoint validation of authentication and authorization logic. Uniform enforcement across all routes is critical.
GraphQL APIs (Query Flexibility, Hidden Complexity)
GraphQL centralizes communication into a single endpoint. That design reduces visible surface area but increases logical complexity.
Instead of targeting many URLs, attackers craft queries that request deeply nested data structures.
Security testing must examine:
Whether introspection is enabled in production
Whether sensitive fields are protected at the field level
Whether deeply nested queries bypass access checks
Whether query depth and complexity limits are enforced
For example, a user may have permission to access their profile. If nested queries allow retrieval of related administrative objects without restriction, data leakage may occur through indirect paths.
GraphQL testing focuses less on URL enumeration and more on schema analysis and field level authorization validation.
SOAP APIs (XML and Legacy Integration Risks)
SOAP (Simple Object Access Protocol) APIs rely on structured XML messaging. Many enterprise systems still use SOAP for financial, healthcare, or government integrations.
Security risks often arise from:
XML External Entity processing
Improper schema validation
Weak WS Security configuration
Misconfigured authentication headers
Unlike REST or GraphQL, SOAP testing requires careful examination of XML parsing behavior. Improperly secured parsers can allow file disclosure or server-side request forgery through crafted payloads.
Mapping API Security Testing to the OWASP API Top 10
Security testing becomes more effective when aligned with established risk frameworks. The OWASP API Top 10 highlights the most common and impactful API-specific vulnerabilities observed in real-world breaches.
Using this framework during API security testing ensures structured coverage of high-risk areas rather than relying on ad hoc checks.
Broken Object Level Authorization (BOLA)
BOLA occurs when an API fails to verify that a user owns or is permitted to access a specific object.
What to test:
Modify object identifiers in URLs or request bodies
Access resources across tenant boundaries
Retrieve data using sequential ID enumeration
Failure example: Changing /api/orders/1001 to /api/orders/1002 returns another user’s order details without ownership validation.
Broken Authentication
Authentication failures allow attackers to impersonate users.
What to test:
JWT signature validation
Token expiration handling
Weak API keys
Insecure password reset flows
Multi-factor authentication bypass
Failure example: Accepting expired tokens or failing to verify token signatures.
Broken Function Level Authorization (BFLA)
BFLA allows users to access restricted functions, often administrative endpoints.
What to test:
Access admin routes with standard user roles
Modify role parameters in requests
Invoke hidden endpoints directly
Failure example: A regular user successfully calling /api/admin/export.
Excessive Data Exposure
APIs sometimes return more data than required. Frontend filtering does not compensate for server side overexposure.
What to test:
Hidden response fields
Internal identifiers
Sensitive attributes such as PII
Debug or metadata fields in production
Failure example: Returning password hashes or internal database IDs in JSON responses.
Lack of Resources and Rate Limiting
Without throttling controls, APIs are vulnerable to automation-based abuse.
What to test:
Login endpoint brute force resistance
Enumeration attempts
Large batch request handling
Query complexity limits
Failure example: Unlimited login attempts enabling credential stuffing attacks.
Security Misconfiguration
Improper configuration exposes APIs unnecessarily.
What to test:
Debug mode in production
Unrestricted CORS policies
Default credentials
Misconfigured API gateways
Failure example: Allowing any origin through a permissive CORS configuration.
Injection Vulnerabilities
APIs process structured input. Weak validation enables injection attacks.
What to test:
SQL and NoSQL injection
Command injection
XML injection
Server Side Request Forgery (SSRF)
Failure example: Database queries built directly from user-supplied parameters.
Improper Assets Management
Organizations often lose track of API versions and endpoints.
What to test:
Deprecated APIs still accessible
Inconsistent authentication across versions
Forgotten development endpoints
Failure example: A legacy version lacking updated authorization controls remains publicly reachable.
A Structured API Security Testing Methodology
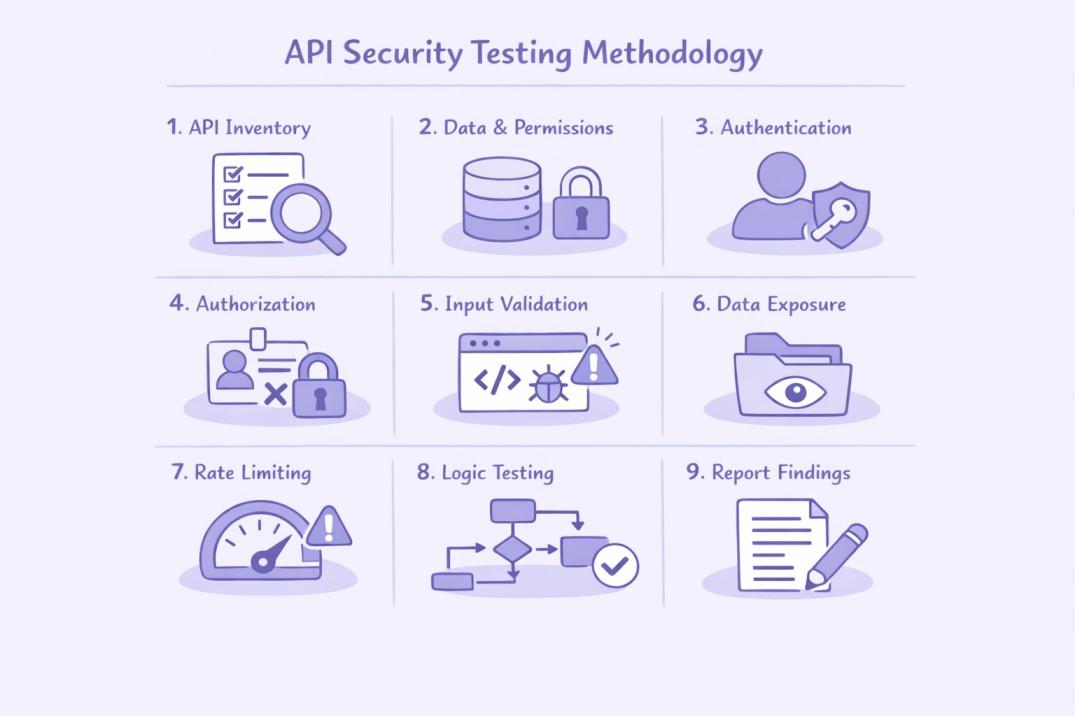
API security testing becomes effective when it follows a repeatable path. Random testing creates false confidence.
A good methodology answers three questions in order:
What APIs exist?
Who can do what?
What happens when someone tries to break the rules?
Below is a simple, field tested workflow you can apply to REST and GraphQL APIs.
Step 1: Build a Real API Inventory
Start by listing every API that can be reached, not just what is documented.
Capture:
Public endpoints used by web and mobile apps
Internal service to service endpoints
Partner or integration endpoints
Legacy versions still responding
Staging or debug endpoints exposed by mistake
Pull from multiple sources: OpenAPI or Swagger files, API gateway logs, reverse proxies, and observed traffic.
Note: API documentation describes what should exist. Logs and reachable routes show what actually exists.
Step 2: Understand the Data and Permission Model
Before you test, map what the API is protecting.
Define:
Key objects: users, orders, invoices, tickets, files, records
Ownership rules: who owns which object
Roles: user, manager, admin, support, partner
Tenants: how customer accounts are separated
Create a small table for yourself: Object → Allowed actions → Allowed roles → Ownership rule.
Remember: Most severe API breaches happen when object ownership is assumed instead of enforced.
Step 3: Validate Authentication Controls
Authentication proves identity. Weak identity checks turn every endpoint into a public endpoint.
Test:
Token validation for JWT or session tokens
Signature checks and accepted algorithms
Expiration and refresh handling
API key scope and rotation behavior
Login and password reset flows
Try realistic failure cases: expired token reuse, missing token, altered JWT claims, reused tokens across accounts.
Tip: Focus on server behavior. Client apps can hide problems. APIs cannot.
Step 4: Test Authorization Where It Fails Most Often
Authorization decides access. API incidents commonly trace back to BOLA and BFLA.
Run targeted checks:
Change object IDs in URLs and request bodies
Access another user’s object inside the same role
Call admin endpoints as a normal user
Modify role or permission fields in requests
Test tenant boundaries with cross account identifiers
Use simple questions:
“Can I access someone else’s record?”
“Can I do an admin action without being an admin?”
“Can I access data across tenants?”
Note: Authorization must be verified at every endpoint. One weak route can expose the whole dataset.
Step 5: Break Input Validation on Purpose
APIs accept structured input. Testing must confirm strict validation, not best effort parsing.
Test for:
SQL and NoSQL injection patterns
SSRF via URL parameters
Mass assignment through unexpected fields
Type confusion such as string vs integer
Oversized payloads and malformed JSON
XML risks for SOAP such as XXE
Add fields that should not be accepted. Change data types. Send boundary values.
Remember: A secure API rejects unexpected input, not silently accepts it.
Step 6: Check Response Data Exposure
Many APIs leak data without “hacking.” They simply return too much.
Review responses for:
Hidden fields not needed by the client
Internal identifiers and metadata
PII such as phone, email, address
Tokens, secrets, debug flags
Admin only attributes visible to standard users
Confirm field level authorization for sensitive attributes.
Tip: Compare what the client needs vs what the API returns. Any extra field is risky.
Step 7: Test Rate Limits and Abuse Resistance
APIs are built for automation. Attackers exploit that with speed and volume.
Validate:
Login throttling and lockouts
Enumeration resistance on ID based endpoints
Rate limits per user, token, and IP
GraphQL query depth and complexity limits
Protection against scraping and bulk export
Send controlled bursts to confirm throttling triggers and error handling.
Note: Weak rate limiting turns small flaws into large incidents.
Step 8: Test Business Logic and Workflow Rules
Automated scanners miss logic abuse. Manual thinking is required.
Test workflows such as:
Checkout and pricing
Refund and cancellation
Discount and coupon rules
Account recovery and verification
“Step skipping” in multi step processes
Try changing the order of requests. Try repeating “one-time” actions. Try skipping validation steps.
Remember: Business logic issues look valid to the API unless the API enforces the rule.
Step 9: Record Findings Like a Developer Would Fix Them
Good results require actionable reporting.
Include:
Endpoint, method, and required headers
Exact request and response evidence
Steps to reproduce
Impact in plain language
Severity based on exposure and exploitability
Fix guidance such as ownership checks, schema validation, rate limiting updates
Tip: A short, reproducible proof beats a long report.
Automated vs Manual API Security Testing
API security testing requires both automation and human analysis. Each serves a different purpose. Using only one leaves gaps.
Automation provides breadth. Whereas, manual testing provides depth.
What Automated Testing Is Good At?
Automated tools are effective for repeatable and pattern-based checks such as:
SQL and NoSQL injection detection
Missing security headers
Basic misconfigurations
Large scale endpoint scanning
Regression testing inside CI/CD pipelines
Automation improves speed and consistency. It works well for known vulnerability categories and continuous validation.
Note: Automated scanners detect technical patterns. They do not understand business rules or context.
Where Automation Falls Short?
Automated tools struggle with logic and permission flaws, including:
Broken Object Level Authorization (BOLA)
Cross tenant data access
Privilege escalation
Multi step workflow bypass
Business logic abuse
Why Manual Testing Is Necessary?
Manual API security testing focuses on how endpoints interact and how rules can be bypassed.
It examines:
Object ownership enforcement
Role boundary consistency
Workflow integrity
Sensitive field exposure
Abuse scenarios at scale
For example, a tester may:
Enumerate predictable user IDs
Access unauthorized records
Extract data repeatedly due to weak rate limits
When Should API Security Testing Be Performed?
API security testing should be driven by change and risk, not by a fixed calendar.
Test an API whenever one of the following occurs:
A new API is being built or exposed publicly
A new endpoint or version is released
Authentication logic changes (JWT, OAuth, API keys)
Role or permission models are updated
A third party integration is added
Infrastructure or API gateway configuration changes
Any modification to identity, access control, or exposure boundaries can introduce new vulnerabilities.
High risk APIs require more frequent testing. Examples include:
Payment processing APIs
Healthcare or PII heavy systems
Multi tenant SaaS platforms
Public APIs with high traffic
Long lived APIs should also be reviewed periodically to detect:
Deprecated but still accessible endpoints
Inconsistent authorization across versions
Security drift over time
After a security incident involving authentication or data exposure, expanded API testing is necessary to confirm similar weaknesses do not exist elsewhere.
API security testing should follow the lifecycle of the system. When the API changes, testing should follow.
Who Should Perform API Security Testing?
API security testing requires technical depth. It is not only a developer task and not only a compliance checkbox. The right expertise depends on system complexity and risk level.
In most organizations, responsibility is shared.
Internal Security Engineers
Security engineers or DevSecOps teams are often best positioned to perform structured API security testing.
They understand:
Authentication architecture
Role and permission models
Multi tenant boundaries
Infrastructure configuration
Developers with Security Training
Developers who build the API should validate:
Authorization enforcement at the endpoint level
Schema validation rules
Object ownership checks
Rate limiting implementation
Independent Penetration Testers
For high risk systems, external security specialists provide an unbiased assessment.
They simulate real attacker behavior and often identify:
Authorization bypass patterns
Logic flaws
Chained exploitation scenarios
Cross tenant access issues
Red Team or Adversarial Simulation Teams
Larger organizations may use red teams to test real-world abuse scenarios.
These teams evaluate:
How vulnerabilities chain together
How far access can escalate
Whether monitoring detects abuse
How API Security Testing Supports Compliance?
Regulatory frameworks increasingly focus on how applications protect data at the interface level. APIs often act as the primary entry point to sensitive systems. Testing those interfaces helps demonstrate that security controls are not only documented, but enforced.
Compliance is not the goal of API security testing. It is a byproduct of doing it correctly.
Demonstrating Access Control Enforcement
Frameworks such as SOC 2 and ISO 27001 require evidence that access to sensitive data is restricted based on role and necessity.
API security testing provides that evidence by validating:
Role based access control implementation
Object ownership enforcement
Multi tenant isolation
Administrative function protection
Protecting Sensitive and Regulated Data
Standards such as PCI DSS, HIPAA, and GDPR emphasize protection of payment data, health information, and personally identifiable information.
API security testing helps verify:
Proper authentication before data retrieval
Data minimization in responses
Protection against injection attacks
Rate limiting to prevent automated data extraction
Supporting Audit and Risk Assessments
Auditors often request proof that security controls are tested and validated.
Structured API testing produces:
Documented test cases
Reproducible findings
Severity classification
Remediation tracking
Reducing Regulatory Exposure
Many compliance failures originate from excessive data exposure or broken authorization at the API layer.
Regular API security testing reduces the likelihood of:
Reportable data breaches
Unauthorized cross tenant access
Exposure of regulated records
Audit findings related to weak access control
Practical API Security Testing Checklist
For readers who need a quick reference, the checklist below summarizes the most important validation points. Each item reflects common failure patterns seen in real world API incidents.
Use it as a verification guide, not a substitute for structured testing.
Identity and Authentication
Are JWT signatures validated with strong algorithms?
Are expired or tampered tokens rejected?
Are OAuth scopes enforced correctly?
Are API keys restricted and rotated properly?
Is multi factor authentication protected against bypass?
Authorization and Access Control
Can object identifiers be modified to access other users’ data?
Are administrative endpoints restricted by role?
Is multi tenant isolation enforced consistently?
Are ownership checks performed server side for every request?
Input and Validation Controls
Are all inputs validated against strict schemas?
Are unexpected JSON fields rejected?
Is protection in place against SQL, NoSQL, or command injection?
Are type mismatches and boundary values handled safely?
Response and Data Exposure
Does the API return only necessary fields?
Are sensitive attributes filtered properly?
Are debug flags and internal identifiers removed in production?
Is field level authorization enforced for sensitive data?
Abuse Resistance and Rate Limiting
Are login endpoints protected against brute force attempts?
Are object enumeration attempts throttled?
Are rate limits applied per user, token, and IP where appropriate?
Are GraphQL query depth and complexity limits configured?
Business Logic and Workflow Integrity
Can multi step processes be skipped?
Can payment amounts or discount values be manipulated?
Are state transitions validated on the server?
Are one time actions enforceably one time?
Frequently Asked Questions
Is API Security Testing Part of VAPT?
Yes. API security testing is typically included within Vulnerability Assessment and Penetration Testing (VAPT). Modern VAPT engagements should explicitly evaluate API endpoints, especially for Broken Object Level Authorization, authentication flaws, and business logic abuse.
How Is API Security Testing Different From API Testing?
API testing verifies functionality and performance. API security testing verifies resilience against misuse. Functional testing checks whether the API works. Security testing checks whether it can be abused.
How Often Should APIs Be Security Tested?
Testing should follow change frequency and exposure level. Public APIs handling sensitive data require testing during development, before major releases, and periodically in production. High-risk systems may require continuous validation.
Do GraphQL APIs Require Different Testing?
Yes. GraphQL requires validation of schema exposure, field-level authorization, and query complexity limits. Unlike REST APIs, testing focuses on query structure rather than endpoint enumeration.
What Is the Most Common API Vulnerability?
Broken Object Level Authorization is one of the most frequently exploited API weaknesses. It occurs when object ownership validation is missing or inconsistent.
Can Automated Scanners Detect All API Security Issues?
No. Automated scanners detect pattern-based vulnerabilities such as injection and misconfiguration. They rarely identify business logic flaws or complex authorization failures without manual review.