API scanning has a fundamental problem: it was built to find what it already knows. In a threat landscape where attackers increasingly exploit business logic gaps, authentication edge cases, and multi-step abuse chains, a signature-based scanner is often the last tool you want to rely on.
This guide breaks down the most effective API scanning alternatives available today, when to use each, how they complement traditional scanning, and how to build a layered strategy that actually reflects how attackers think.
Why API Scanning Alone Isn't Enough?
The case for API scanning is simple: it's fast, automated, and scales across hundreds of endpoints with minimal configuration. For detecting common issues like injection flaws, schema violations, and open endpoints, it does the job. But that's roughly where its usefulness ends for organizations running complex, high stakes APIs.
According to Gartner's 2025 Application Security research, APIs have become the most frequently targeted application layer, with API-specific attacks accounting for a majority of web application incidents. Meanwhile, Salt Security's State of API Security Report found that 95% of organizations experienced API security problems in the prior 12 months, and most were missed by automated scanning alone.
The core limitation isn't the tool, it's the methodology. Scanners are rule based. They don't understand context. They can't model the difference between a valid privileged request and an attacker who has legitimately authenticated but is now abusing their access. They don't know that your /admin/export endpoint should only be reachable after three specific preceding calls in a session.
This is exactly the kind of gap that leads to breaches.
What Traditional API Scanners Miss?
Before evaluating alternatives, it helps to be specific about where automated scanners fall short. The limitation isn't just "they miss some things", it's structural.
Business logic flaws are the clearest example. These aren't vulnerabilities in the traditional sense, there's no malformed payload or injection string. The flaw is in the workflow itself: a price manipulation that skips a validation step, an order that can be duplicated by re sending a specific sequence of calls, a coupon code that can be applied indefinitely. No scanner can flag this without understanding what the application is supposed to do.
Multi step and chained request attacks present a similar problem. Privilege escalation through BOLA (Broken Object Level Authorization) often requires several legitimate-looking requests made in sequence. A scanner testing endpoints in isolation will never surface this.
Authentication and authorization edge cases are frequently missed. Scanners may check for missing auth headers, but typically don't model the full scope of role-based access control, token reuse, JWT manipulation, or the kinds of API authentication and authorization vulnerabilities described in the OWASP API Top 10, the industry's primary reference framework for API-specific risk.
Broken Object Level Authorization (API1), Broken Authentication (API2), and Broken Function Level Authorization (API5) in particular demand context-aware testing that automated tools can't reliably deliver.
Shadow APIs and undocumented endpoints are another consistent blind spot. Scanners typically work from a known schema or endpoint list. APIs that were never formally documented, legacy endpoints, testing routes left in production, third-party integrations that weren't inventoried, sit entirely outside the scanner's view.
The Best API Scanning Alternatives
1. Manual API Penetration Testing
The most direct replacement for scanner depth is skilled human testing. Structured API pentest methods involve a security engineer or red team member mapping the API's attack surface, reviewing authentication flows, testing for access control issues, and probing business logic in ways that mirror real attacker behavior.
The key advantages over automated scanning are depth and adaptability. A penetration tester can recognize when an API's response to a manipulated parameter suggests a deeper vulnerability, follow that thread across multiple endpoints, and validate actual exploitability — not just theoretical exposure.
When it's the right choice: Before major releases, after significant architecture changes, for APIs handling regulated or sensitive data, and as part of any meaningful security audit. It is resource-intensive and not continuous by nature, which is why it should be combined with other approaches rather than used in isolation.
When evaluating coverage, it's worth understanding the differences between API scan vs API pentest approaches: scanning gives you breadth across known patterns quickly; penetration testing gives you depth against real-world attack scenarios on critical targets.
2. API Security Testing in CI/CD Pipelines
Embedding API security testing in CI/CD pipelines is one of the highest-leverage changes an engineering organization can make. Rather than running assessments as periodic events, security tests execute with every code push, surfacing vulnerabilities at the moment they're introduced, when they're cheapest to fix.
This shift left approach typically combines lightweight automated tests (schema validation, regression checks for known vulnerability classes) with policy as code controls that fail builds when security criteria aren't met. Tools in this category integrate with platforms like GitHub Actions, GitLab CI, and Jenkins, and can enforce rules derived from API schema validation and fuzzing pipelines against every new endpoint or payload structure.
The practical benefit: A vulnerability caught in a developer's pull request takes minutes to fix. The same vulnerability caught in a post-production scan takes days of coordination, incident review, and potentially public disclosure. The math strongly favors early detection.
When it's the right choice: Organizations running continuous deployment cycles, API-first product teams, and any team that has experienced production vulnerabilities traced back to an unreviewed code change.
3. API Fuzzing
API schema validation and fuzzing explained simply: fuzzing means deliberately sending malformed, unexpected, or boundary-crossing inputs to API endpoints to see how they behave under stress. Unlike scanning, which checks against known patterns, fuzzing discovers unknown failure modes.
Modern API fuzzing tools can generate test cases from OpenAPI/Swagger specifications, automatically mutating valid request structures to find crashes, unexpected behavior, and input validation gaps. This makes it particularly effective for finding:
Memory corruption or parser bugs
Unhandled edge cases that could cause denial of service
Input fields that accept values outside their intended range
Endpoints that behave differently under high input volume
Fuzzing shines in the space between "this configuration is wrong" (scanner territory) and "this business logic is broken" (penetration testing territory). It finds the messy middle — where the code does something technically valid but operationally dangerous.
When it's the right choice: As part of a CI/CD pipeline for APIs that accept complex user input, for APIs built on custom parsers or serialization logic, and alongside spec-driven testing where you want to validate that the implementation matches the contract.
4. Runtime API Protection
Deploying runtime monitoring means you're watching API behavior in production rather than only testing it before deployment. This category includes API gateways with behavioral analytics, WAFs tuned for API traffic patterns, and dedicated API security platforms that build a behavioral baseline and alert on or block deviations.
The protection model here is different from all other approaches on this list. You're not finding vulnerabilities before they're exploited; you're detecting exploitation attempts as they happen. This is meaningful because some vulnerabilities only emerge under real-world conditions, zero-day issues, novel abuse patterns, or API endpoints that interact unexpectedly with live data.
Runtime protection also provides critical visibility into API authentication and authorization vulnerabilities that appear only in production traffic, token reuse across sessions, abnormal access patterns that suggest credential stuffing, or endpoints seeing traffic volumes inconsistent with known client behavior.
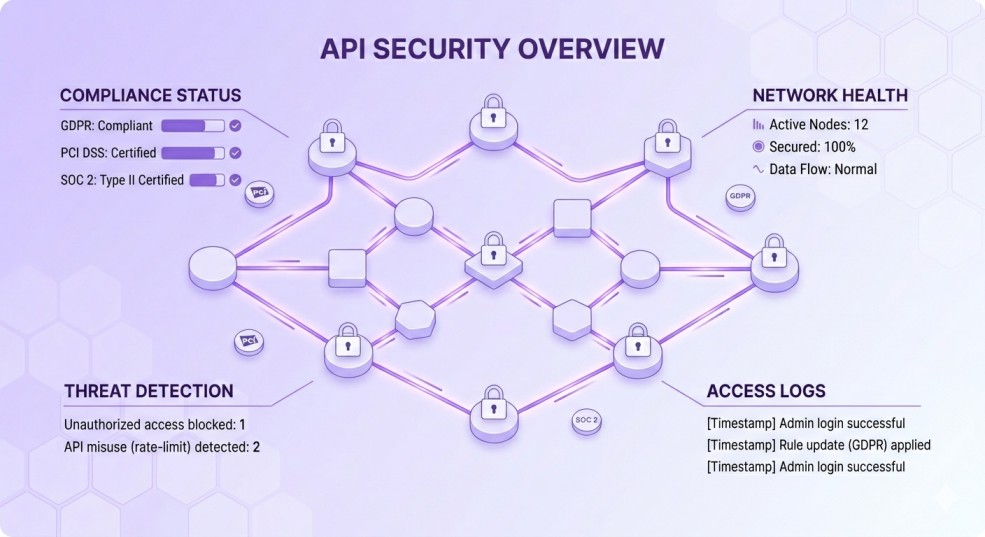
When it's the right choice: For production APIs handling sensitive data, as a defense-in-depth layer alongside pre-deployment testing, and in regulated industries where detection and response SLAs matter for API security compliance for PCI DSS, GDPR, and SOC 2 requirements.
5. Attack Surface Management for APIs
Organizations with large, distributed, or microservices-heavy architectures often have a simple but serious problem: they don't know exactly how many APIs they're running. Attack Surface Management (ASM) tools address this by continuously scanning external facing infrastructure to discover APIs that weren't formally inventoried.
The value isn't just discovery, it's ongoing monitoring. An ASM platform can alert when a new API endpoint appears on a subdomain, when an internal service is accidentally exposed, or when a forgotten staging environment becomes publicly accessible. Given that many significant breaches trace back to undocumented APIs that were simply never secured because nobody knew they existed, this visibility is foundational.
When it's the right choice: Any organization that runs microservices, uses multiple cloud providers, or has API endpoints spread across product teams without centralized governance.
6. Red Teaming for API Security
Red teaming is the adversarial simulation tier of API security. Unlike penetration testing, which typically follows a defined scope and methodology, red teaming is goal-oriented: the team is given an objective (exfiltrate customer data, escalate privileges to an admin role, disrupt a transaction workflow) and given latitude to pursue it using realistic attacker techniques.
This means combining API security scanning tool output with open source intelligence, credential enumeration, social engineering of developer documentation, and chained exploitation of minor issues that wouldn't individually trigger alerts. The goal is to find what an actual threat actor would find, not what a compliance checklist would flag.
Red teaming produces findings that are qualitatively different from other approaches: not a list of vulnerabilities with CVSS scores, but a narrative of how your API ecosystem can be compromised from the outside, what detection gaps exist, and how long an attacker could persist undetected.
When it's the right choice: Mature security programs, organizations with high-value APIs (financial services, healthcare, identity platforms), and companies that have already addressed findings from standard penetration testing and want to validate their detection and response posture.
7. Bug Bounty Programs
Bug bounty programs extend your testing coverage to a global community of security researchers working under coordinated disclosure agreements. Researchers test APIs against real infrastructure using their own tooling and techniques, and report valid findings in exchange for financial rewards.
The key differentiator from internal testing is cognitive diversity. A researcher who has found authentication bypass patterns across dozens of different platforms will bring pattern recognition that no internal team can fully replicate. They approach your API the way an attacker would, without knowing your codebase, without assumptions about what should be secure, and with strong incentives to find what others missed.
When it's the right choice: As a complement to internal penetration testing, for public facing APIs that process high-value data, and for organizations that want continuous external validation without the overhead of a full-time external red team.
How to Match the Right Approach to Your Risk Profile?
No single approach is universally correct. The right combination depends on what you're protecting, how fast it changes, and what your threat model actually looks like.
Start with your data sensitivity
APIs handling payment card data, healthcare records, or personal identity information operate under specific regulatory obligations. API security compliance for PCI DSS, GDPR, and SOC 2 frameworks each have testing requirements, PCI DSS 4.0 explicitly requires authenticated penetration testing of API endpoints, while SOC 2 auditors increasingly expect evidence of continuous security monitoring rather than annual point-in-time assessments.
Factor in deployment velocity
Teams shipping multiple times per day can't rely on quarterly penetration tests as their primary security signal. API security testing in CI/CD pipelines becomes essential, it's the only approach that keeps pace with continuous deployment.
Assess your known vs. unknown surface area
If you have high confidence in your API inventory and architecture, scanning and penetration testing can focus on known endpoints. If you're running a large microservices estate or have historically poor API governance, Attack Surface Management should be a prerequisite before you invest heavily in depth testing of individual APIs.
Consider your detection maturity
The value of runtime protection and red teaming depends heavily on whether you have the monitoring infrastructure to act on what they surface. If you don't have meaningful API logging or anomaly detection in place, building that foundation should precede investment in advanced adversarial simulation.
Where API Scanning Still Earns Its Place?
None of this means abandoning API scanning. For its intended use cases, fast, broad coverage identification of known vulnerability classes, schema conformance, and configuration errors, it remains valuable.
API security scanning tools are most effective as the baseline layer of a defense in depth strategy: running continuously, integrated into development workflows, and providing the breadth coverage that manual testing can't economically replicate at scale. The OWASP API Top 10 provides a useful framework here, categories like Excessive Data Exposure (API3) and Security Misconfiguration (API7) are exactly the kind of issues that scanning tools reliably surface.
The mistake is treating scanning as a sufficient security measure rather than a necessary starting point. A scan that comes back clean doesn't mean your API is secure, it means it doesn't have the specific issues the scanner knows how to find. That's a much narrower claim.
A Layered API Security Strategy
The organizations with the strongest API security postures aren't using one tool exceptionally well. They're layering complementary approaches so each gap in one method is covered by another.
A practical layered model looks like this:
Foundation layer, continuous automated coverage: API scanning and schema-based fuzzing run in CI/CD, with ASM monitoring the external attack surface for undocumented endpoints.
Validation layer, depth testing at key milestones: Penetration testing using structured API pentest methods at major releases, architecture changes, and compliance review cycles. This is where API authentication and authorization vulnerabilities get properly tested against the full scope of role and permission scenarios.
Production layer, runtime visibility and response: Behavioral monitoring and anomaly detection on live API traffic, providing detection capability for attacks that bypass pre-deployment controls.
Adversarial layer, periodic realistic simulation: Red team exercises for high-risk APIs, supplemented by bug bounty programs for continuous external research coverage.
This architecture means that a sophisticated attack targeting a business logic flaw won't be stopped only because a scanner didn't flag it, the penetration test, runtime monitoring, or bug bounty researcher will have multiple opportunities to surface it first.
Final Takeaway
The question isn't whether to replace API scanning, it's how to stop treating it as a complete answer to API security. The OWASP API Top 10, regulatory frameworks like PCI DSS and GDPR, and the actual data on API breach patterns all point toward the same conclusion: modern API security requires a combination of automated breadth, human depth, continuous monitoring, and adversarial simulation.
The tools to build that combination exist today. The organizations that invest in layering them, rather than relying on any single approach, are the ones whose APIs remain secure as they scale.